### Patent Pending: Securing the Innovation Born from Valley Necessity — What SmiteByte’s IP Fortress Means for Customers and the Future
Last week we published “Plato Was Right — Necessity Is the Mother of Invention… and She Refused to Leave Until We Built the Blackbox at 3 a.m. in Imperial County.” That piece told the origin story: a 100-year-old agricultural operation — one of our longest-standing customers — was compromised by sophisticated attackers who slipped through everyday trusted websites, gained admin rights, disabled defenses, and moved laterally across the network with zero alerts. The first visible sign was a mouse cursor moving on its own. The expensive, cloud-connected tools that were supposed to protect them had failed to see what was happening inside the building.
Necessity didn’t send a procurement request or wait for a vendor roadmap. She sat us down at 3 a.m. and demanded we build something better.
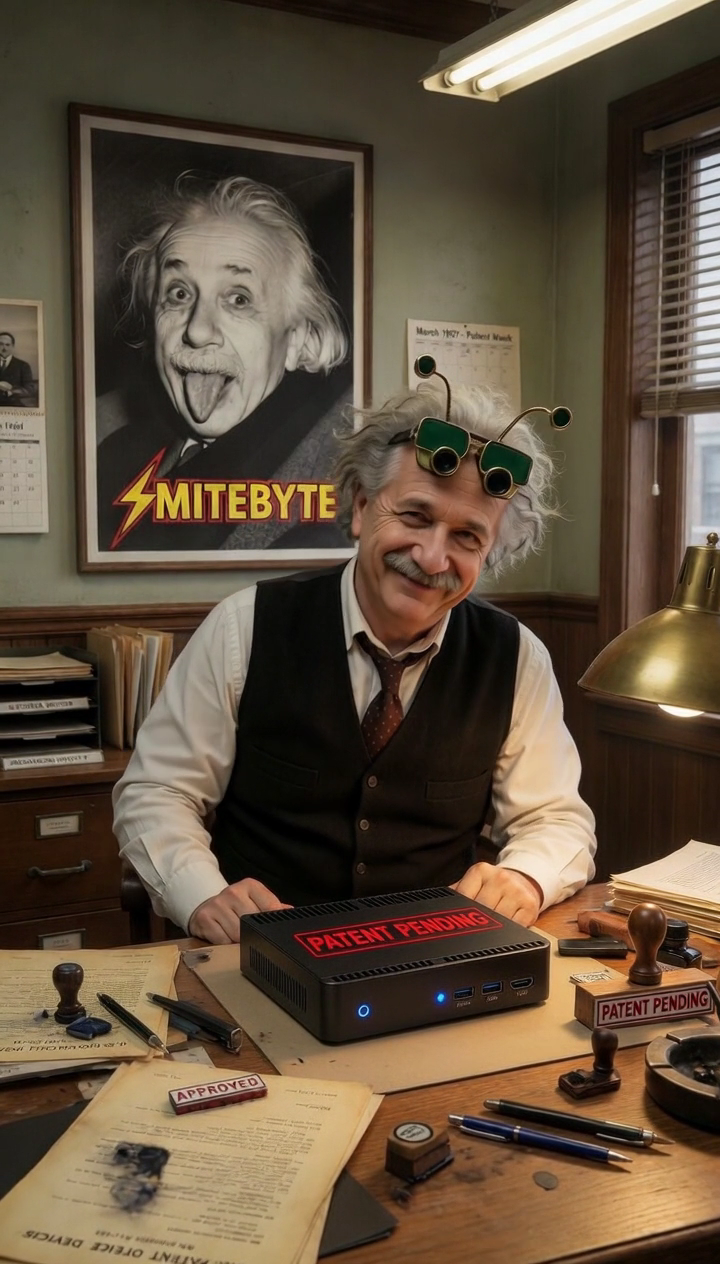
On April 13, 2026, we filed our provisional patent. The SmiteByte Blackbox NDR system is now officially Patent Pending.
This filing, layered with our trademark, copyright protection on our correlation methodology, and strict trade secret controls on implementation details and deployment playbooks, creates a complete intellectual property fortress around the specific method we invented.
### Why This Matters — From Every Relevant Angle
For the businesses we serve
Most network security solutions today are built for enterprises with dedicated security teams, six-figure budgets, and tolerance for ongoing vendor relationships. They phone home to the cloud, generate endless dashboards, and require analysts to interpret alerts. Small and mid-sized operators — the diversified farm owners, urgent care centers, dental practices, schools, and multi-location businesses that form the backbone of places like Imperial County — are left with either overpriced MSP contracts or tools that simply don’t fit.
SmiteByte was built the opposite way: agentless, on-premises only, zero cloud telemetry, zero recurring software fees, and a single plain-English morning report delivered directly to the person ultimately responsible for the business. The patent now formally recognizes that this complete delivery model — the way we correlate multiple streams of network intelligence, resolve raw addresses into human-readable identities, apply weighted threat scoring, group assets under real owners and departments, and produce actionable reports without external dependency — is novel and protectable.
For the competitive landscape
Darktrace, Vectra, ExtraHop, Corelight, and the major EDR platforms all rely on cloud connectivity, subscription revenue, and (in most cases) agents or external analysts. Their pricing starts in the high five or six figures annually and scales with data volume or modules. Our model replaces those entire relationships with a one-time hardware purchase plus modest annual renewal for equipment refresh.
The patent protects the precise orchestration that makes this replacement possible at SMB price points. Trade secrets guard the calibration methodologies and deployment playbooks that let us bring a fully operational Blackbox online for any customer with exceptional speed and precision. This combination creates a durable moat: competitors can see the individual components, but they cannot replicate the integrated, human-first delivery system without infringing the protected method.
It also aligns with our core doctrine: Think small, move big. No cloud. No telemetry. No subscriptions. No apologies. The IP stack reinforces that doctrine by making the alternative to the dominant cloud/MSP model legally defensible.
For long-term value and scalability
The protected architecture gives us a clear path to continue evolving the Blackbox with smarter local intelligence capabilities while remaining fully on-premises and aligned with our core doctrine.
For the operators who built this
This protection is an act of stewardship — safeguarding a solution born from real necessity in Imperial County so it can continue serving the operators who actually run the businesses that keep communities like the Valley alive. We did not build this to chase headlines or play defense. We built it because the breach was coming from inside the building, and the tools that were supposed to catch it didn’t.
### The Bottom Line
When you choose SmiteByte, you are not investing in a commodity appliance that could be copied or discontinued. You are investing in a protected method engineered specifically for operators who need visibility without complexity, cost, or loss of control.
The network breach is still coming from inside the building.
But now the defense that watches from inside — the one that speaks plain English, keeps every byte on your premises, and requires no external analysts or cloud accounts — is formally protected.
Patent Pending — Filed April 13, 2026
SmiteByte — We Watch Your Computer Network So You Don’t Have To.
Built in Holtville, California.
Protected for the operators who actually run the businesses.
-Paul @ Smitebyte
###