Plato Was Right — Necessity Is the Mother of Invention… and She Refused to Leave Until We Built the Blackbox at 3 a.m. in Imperial County
Reader,
There's a saying most people half-remember from school: necessity is the mother of invention (as Plato put it). What it actually means is simpler than it sounds. Nobody builds something genuinely new because they had extra time and resources. They build it because they had no other choice.
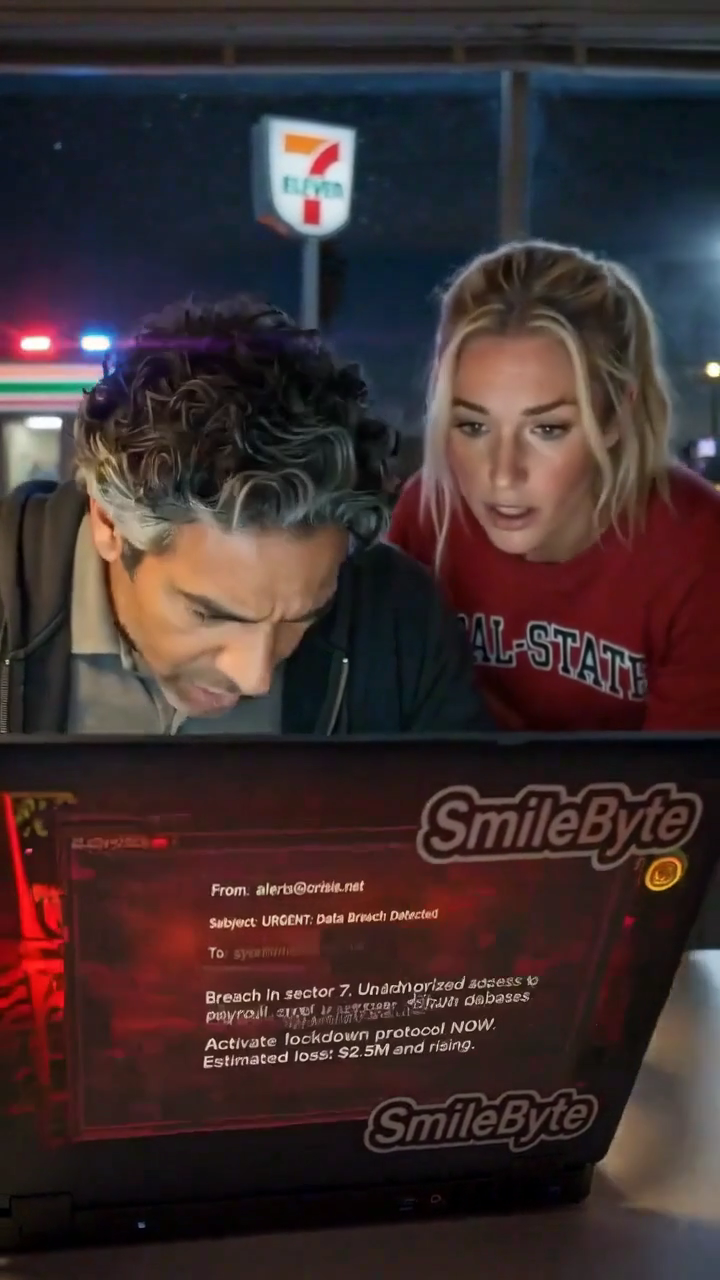
SmiteByte was built out of necessity. A customer — a real operation, 100 years old, with the best equipment and software money could buy — got hit. State-level attack tools slipped in through trusted everyday websites. They moved silently from device to device across the entire network without triggering a single alert. The first sign anything was wrong was a mouse moving on a screen nobody was touching.
The tools that were supposed to catch it didn’t. Not because they were bad tools. Because they were watching the wrong door. Firewalls and antivirus watch the perimeter — what comes in from outside. They don’t watch what happens inside, between your own computers, your own devices, your own network. That’s the blind spot. That’s where the damage happened.
We didn’t call a vendor. We didn’t open a procurement process. We didn’t schedule seventeen meetings to align stakeholders on a solution framework. There was no trouble ticket to open, no one to call, no help desk on the other end. No one left but us to figure this entire thing out. So we sat down, got desperate, and built something.
That’s the part they never tell you about necessity being the mother of invention. They make it sound noble. What it actually looks like is a man at a keyboard at 3 a.m. muttering about log files while his coffee goes cold, too stubborn to admit he doesn’t know what he’s doing yet, too angry about what happened to stop — with his wife right there beside him, guiding every line of code.
That’s where SmiteByte came from. Not a whiteboard. Not a pitch deck. Desperation and a deadline that nobody set but us.
So we built something to watch the inside.
What We Built and Why It’s Different
The SmiteByte Blackbox correlation engine does something that sounds simple but isn’t. It takes independent data streams from across your network and fuses them into a single weighted risk picture for every device. Every morning at 6 a.m. that becomes one plain-English email that tells a non-technical business owner exactly what happened the night before and what actually matters.
No dashboards. No analysts. No cloud. No subscriptions.
The piece that makes it readable — the piece that took the longest to get right — is the device identity translation layer. Every IP on your network gets resolved to a human name before anything is reported. Not 192.168.1.47. Bob’s laptop. Not 192.168.1.23. Front gate camera. A business owner who has never seen a network diagram can read this report and understand it immediately.
That translation layer, combined with the correlation and scoring logic, is what we formally registered with the United States Copyright Office as a proprietary computer program this month. Case #1-15138791601 is on file. Priority date established April 9, 2026.
Why This Matters — And Why We’re Talking About It
We’re not talking about this to impress anyone. We’re talking about it because future partners and customers reasonably ask: is this original work or just open-source tools glued together?
The foundation tools are open source. We’ve never hidden that. But the way they are fused, scored, translated into human terms, and delivered as actionable morning truth to non-technical operators — that’s ours. Built here. In Holtville, California. Imperial County — the unemployment capital of the United States.
Nobody funded this. No venture capital. No Fortune 1000 payroll. Just a problem that needed solving, deep experience, and the kind of fire that comes from watching something preventable happen to people you care about.
Corelight and Darktrace run similar base tools but are built for large enterprises in the energy sector, public utilities, and organizations with million-dollar budgets. They require ongoing subscriptions, cloud connectivity, and either dedicated analysts or their managed service offerings — none of which fit the needs of small and mid-size businesses like local CPA firms, medical practices, or agricultural operations.
SmiteByte starts at $9,999. One time. No analyst required. No cloud. No subscriptions. Ever.
The difference isn’t the ingredients. The difference is the recipe. And the recipe is protected.
Protecting What We Built
We formally registered the SmiteByte Blackbox correlation engine — including the device identity translation layer, the weighted multi-source scoring logic, the beacon detection thresholds, and the full fusion methodology — with the United States Copyright Office as a proprietary computer program this month. Case #1-15138791601 is on file. Priority date established April 9, 2026.
In addition, the specific correlation logic, exact scoring weights, and device identity methodology are actively protected as trade secrets under U.S. law — the same proven strategy that has kept Coca-Cola’s secret formula guarded for over 130 years. None of this is published. None of it is on GitHub. The scripts do not leave the building and never will.
Equally important, the Blackbox operates in complete silence from the mirror port. No one outside your organization — not employees, not competitors, not anyone — needs to know the full scope of your network monitoring capabilities, whether defensive or offensive. Stealth is part of the protection.
We took these deliberate, formal steps because what we built is genuinely novel and valuable — born from necessity in Imperial County. This dual protection (official copyright registration plus strict trade secret safeguards) was formally established on April 9, 2026 and gives both us and our customers and future partners clear confidence that the unique advantage SmiteByte delivers remains ours alone.
This matters. When you work with SmiteByte, you are investing in original, professionally protected technology that no one else can copy — the kind that quietly delivers real peace of mind to busy owners every single morning.
Innovation Doesn’t Require a Zip Code
If you’re reading this as a potential partner — someone who serves small and mid-size businesses, medical practices, agricultural operations, legal firms, and accounting firms — understand what you’re looking at.
This isn’t a startup with a pitch deck. This is a working product with units in the field, customers who trust it, and a morning report landing in real inboxes every day across Imperial County. Built by one man and his wife. Refined through real deployments. Protected because it’s worth protecting.
We Watch Your Computer Network So You Don’t Have To.
Necessity built it. Imperial County is where it lives.
Whether you run an operation that needs watching or you help businesses like these every day — reach out. I’m right here in the Valley, and I’d be honored to talk.
— Paul and the Mother of Invention @ SmiteByte